SEARCH
The great Apple Pay heist myth
SHARE IT
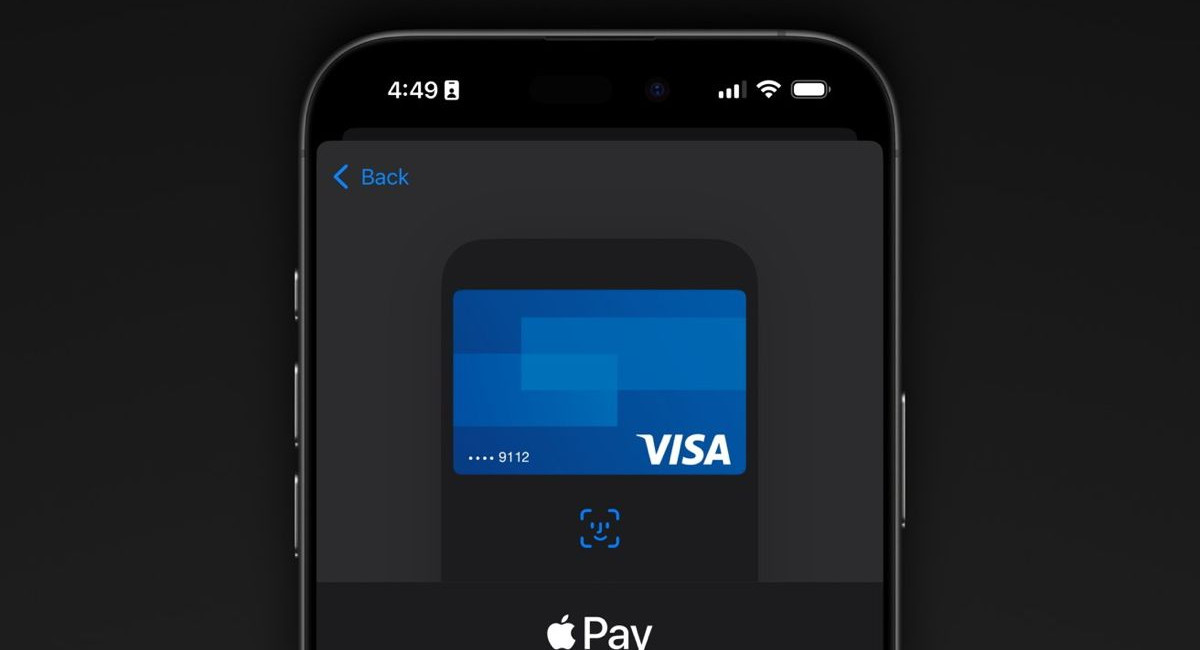
Fear is a powerful tool for generating viral content. Over the past few decades, late night news programs have frequently relied on the "it could happen to you" narrative to boost ratings and keep audiences engaged. YouTube creators are also intimately familiar with this tactic. Recently, prominent technology reviewer Marques Brownlee partnered with the channel Veritasium to demonstrate a scenario where they seemingly stole ten thousand dollars from a locked iPhone. This demonstration utilized a man in the middle attack to intercept the communication handshakes between the smartphone and a payment terminal.
However, it is crucial to clarify the reality of this situation immediately. This digital heist is practically impossible to execute against the average user. There is absolutely no reason to panic, and you do not need to take any evasive action or change your device settings to protect yourself from this highly improbable scenario. The demonstration video may look visually alarming, but the practical application of this exploit is incredibly complex and requires a highly specific set of circumstances.
To understand why you are safe, we must look at the specific requirements of the attack. Fundamentally, this hack requires your locked iPhone to be placed in close proximity to a specialized NFC reader connected to a laptop controlled by the attacker. In practical terms, this means your iPhone must have already been stolen. A hacker cannot perform this extraction remotely while you are simply walking down the street or sitting in a restaurant.
The stringent requirements continue well beyond physical access to the device. For the exploit to function, the user must have a Visa card specifically assigned to the Express Transit feature within the Apple Wallet. The vulnerability exploited here is not a flaw in Apple software or hardware, but rather a specific weakness in the security protocols utilized by Visa. Only if all these rare conditions align, and the attacker initiates a transaction on a compromised payment terminal, will the funds be authorized and transferred.
From a practical standpoint, criminals have far easier and more efficient methods for stealing money using technology. Common techniques like card skimmers installed at gas stations pose a much more realistic threat to everyday consumers, and there is little proactive protection against them. If a criminal is specifically targeting a high net worth individual, this Apple Pay exploit remains a poor choice. The attacker would need a wealthy victim who carries an iPhone, uses a Visa card specifically for Express Transit, and somehow leaves their device completely unattended and accessible.
Even in the incredibly unlikely event that all these stars align and a theft occurs, the victim is not left to absorb the financial loss. Any stolen funds would be fully refunded thanks to standard fraud protection policies maintained by Visa. While reporting the fraud and waiting for the refund is undoubtedly inconvenient, the situation is ultimately resolved without lasting financial damage to the cardholder.
The demonstration video strongly suggests that users should disable the Express Transit feature to protect themselves, while also criticizing Apple for enabling it by default. Security experts largely disagree with this advice. The primary advantage of Express Transit is the ability to pay for public transportation even when the iPhone battery is completely dead. Disabling this feature out of fear of a theoretical threat deprives the user of a highly convenient tool.
The researchers also implied that criminals could easily build discreet, portable devices to execute this attack while the phone remains in a pocket. Based on the technical requirements shown, this is highly unrealistic. The theft device requires prolonged, stable contact during the transaction. Furthermore, the thief would have to perfectly coordinate with an accomplice operating the compromised terminal, all while relying on a local wireless connection.
Ultimately, the most realistic application of this exploit involves a device that is already stolen. A thief would need to snatch the iPhone, escape to a secure location, and execute the complex transaction before the owner realizes the theft and locks the device remotely using the Find My network.
In conclusion, while this represents an interesting technical vulnerability, it is not a reason to change daily habits. The public has known about this specific loophole since the year twenty twenty one, and there has not been a single reported case of mass fraud utilizing this method. Visa maintains that the vulnerability is of such little consequence that the massive engineering effort required to patch it would far exceed the cost of refunding the extremely rare victim. Users can continue utilizing their digital wallets with complete peace of mind.
MORE NEWS FOR YOU

 Help & Support
Help & Support